Controlling the SQL Log Backup Temp Folder
By default, Veeam picks the local disk with the most free space (often C:) and uses a folder like \Veeam\Backup\SqlLogBackup or C:\ProgramData\Veeam\Endpoint\SqlLogBackup to store the native log backup files before copying them to the backup repository
These files are Veeam’s own “.BAK” format (not native SQL .BAK) and are deleted after shipping. However, on heavily-loaded SQL servers this can quickly fill the drive. To prevent this, Veeam provides a registry setting named SqlTempLogPath that lets administrators manually specify an alternate folder for the log backups.
Understanding and using this key ensures log backups don’t crash your SQL server due to a full disk.
The SqlTempLogPath registry value (a REG_SZ string) tells Veeam where to stage SQL transaction log backups on the SQL Server itself.
Its behavior varies by scenario:
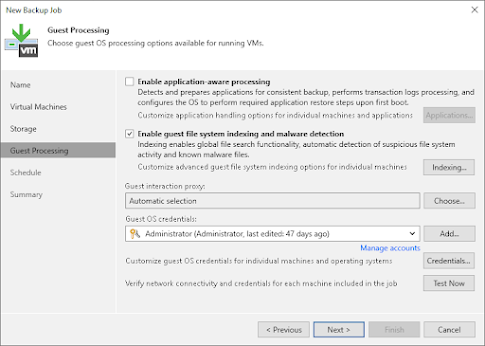
Image-level (VM) backup by Veeam B&R
On the first run of a transaction log child job, Veeam scans all volumes on the SQL VM, picks the one with most free space, and writes that path into the SqlTempLogPath value. To override this default, create or update the registry entry on the SQL host
- Path: HKEY_LOCAL_MACHINE\SOFTWARE\Veeam\Veeam Backup and Replication
- Name: SqlTempLogPath (String)
- Value: <full desired folder path> (no trailing “\”)
For example, to point logs to D:\SqlLogs you could run (as Administrator) the following PowerShell command:
New-ItemProperty -Path "HKLM:\SOFTWARE\Veeam\Veeam Backup and Replication" `
-Name "SqlTempLogPath" -Value "D:\SqlLogs" -PropertyType String
Veeam Agent (Standalone or managed) backups
For machine-level backups using Veeam Agent on Windows, the default temp folder is %ProgramData%\Veeam\Endpoint\SqlLogBackup\. You can override this by setting:
- Path: HKEY_LOCAL_MACHINE\SOFTWARE\Veeam\Veeam EndPoint Backup
- Name: SqlTempLogPath (String)
- Value: <desired folder path> (no trailing backslash)
This registry key goes on the SQL server (the machine running the Agent backup job). (If the job is managed by VBR, the VBR-style path under HKLM\SOFTWARE\Veeam\Veeam Backup and Replication is also acceptable.)
If the SqlTempLogPath is set under the Endpoint Backup key and later becomes invalid, the log backup will fail with an error like “Cannot create folder… Invalid folder path” and the missing intervals will be flagged.
Unlike the VM case, Veeam Agent does not automatically re-pick a drive in that situation; you must correct or remove the key and restart the job.
Cluster-aware backups
For SQL Server on a failover cluster managed by Veeam Agent (VBR-managed AG/FCI), Veeam first checks if the HKLM\SOFTWARE\Veeam\Veeam Backup and Replication key exists.
If it does not, Veeam uses a fixed default folder (C:\ProgramData\Veeam\Backup\SqlLogBackup) on whichever node is active.
If the key exists but SqlTempLogPath is missing or invalid, Veeam picks the largest drive and then records it in SqlTempLogPath for that node.
To manually set a cluster node’s path, create SqlTempLogPath under HKLM\SOFTWARE\Veeam\Veeam Backup and Replication on each node (no trailing slashes).
Note that if you point the path to a cluster disk, a failover might render it invalid: Veeam will then choose a new path and update the registry.
Important
Restart the job
After creating or changing SqlTempLogPath, disable and re-enable (or restart) the SQL backup job. This forces Veeam’s log-shipping process to reload the new setting.
Disk space sizing
Plan ahead – you need enough space to hold the largest log backup between full backups. If you do frequent log backups, the needed temp space is roughly the size of one full backup cycle’s worth of logs (for example, if you back up every 20 minutes and keep a weekly full, you might need tens of GB). The more frequent log jobs = smaller native log chunks
Permissions
Ensure the chosen path is writable by the Veeam services (usually the local System or VeeamService account). Otherwise Veeam will fail to write the logs.
Conclusion
The SqlTempLogPath registry key is a powerful knob for Veeam administrators who need to control where SQL transaction log backups are staged. By default, Veeam chooses the largest local volume, which can be problematic on busy SQL servers. Manually setting SqlTempLogPath lets you relocate the temp files to any local drive or folder with adequate space.